Dede4d is a creeping presence. It hides in the shadows of your system, watching. You might not even know it's there until it's too dangerous. This phantom can drain your precious information, forsaking you in its trail.
- Beware of Dede4d's devious tactics. It may disguise as a innocent program, tricking you into downloading it.
- Be cautious by scanning your system for unfamiliar processes.
- Keep your software updated to strengthen your defenses against Dede4d and similar dangers.
???? Dede4d: A Malware Nightmare Unveiled
Dede4d is a emerging malware threat that's gaining traction. This cyber menace is designed to compromise computer systems, launching DDoS attacks.
Dede4d operates by leveraging zero-day exploits in software and operating systems. Once installed, it can constantly record your device, giving attackers unfettered access over your get more info personal information. The consequences of a Dede4d infection can be severe, leading to data breaches.
It's crucial that users take steps to defend their systems from this dangerous threat.
☠️ Unmasking Dede4d: Inside the Hack
Dede4d, the infamous hacking group, recently made headlines after launching/executing/pulling off a series of high-profile/serious/major attacks on numerous/various/countless targets. Security researchers/Cybersecurity experts/Law enforcement officials have been working tirelessly/scrambling/racing against the clock to uncover/dismantle/expose Dede4d's inner workings and bring them to justice/stop their operation/neutralize their threat.
The group is known for its sophisticated/complex/advanced tactics, techniques, and procedures (TTPs). Their attacks/breaches/intrusions often involve exploiting vulnerabilities/leveraging malware/using social engineering. Dede4d has been linked to/associated with/attributed to several high-profile data breaches/ransomware attacks/cyber espionage campaigns, causing millions/billions/significant in damages/losses/harm.
Analysts/Experts/Researchers believe that Dede4d is a highly organized/well-funded/coordinated group with a global reach/international connections/worldwide operations. Their goals/motives/objectives remain unclear, but they are suspected of operating for financial gain/seeking political influence/spying on governments and corporations.
- Investigators/Authorities/Experts are currently working/actively pursuing/making progress in their investigation into Dede4d.
- Sharing information/Collaborating with other agencies/Providing resources is essential/crucial/vital to combating this growing threat/persistent danger/increasingly sophisticated adversary.
- Staying informed/Being vigilant/Taking precautions can help individuals and organizations protect themselves from cyberattacks/mitigate their risk/avoid becoming victims.
???? Dede4d Attacks: How to Protect Yourself
Dede4d threats are becoming increasingly prevalent, targeting individuals and organizations alike. These harmful acts aim to exploit sensitive data, disrupt networks, and cause financial damage. To defend yourself against Dede4d attacks, it's crucial to implement robust security measures.
- Maintain your software updated to the latest versions.
- Implement strong and unique credentials for all your accounts.
- Be wary of unfamiliar emails and URLs.
- Install reputable antivirus on your devices.
- Inform yourself and your employees about Dede4d attacks and best practices for prevention.
By implementing these tips, you can significantly reduce your risk to Dede4d attacks and defend your valuable information.
????️ Defending Against Dede4d: Security Measures Explained
Dede4d is a malicious threat that can compromise your systems. It's important to use strong security defenses to reduce the risks.
One crucial step is to patch your software regularly. This covers operating systems, applications, and firmware. Security fixes often address known vulnerabilities that Dede4d could exploit.
Another critical measure is to install robust antivirus and anti-malware software. These solutions can help detect Dede4d infections and remove them.
It's also crucial to be wary of phishing attacks. Dede4d often propagates through these schemes. Be sure to confirm the legitimacy of links before clicking on them.
Finally, implementing multi-factor authentication (MFA) can add an extra layer of protection. MFA requires users to provide multiple forms of confirmation, making it more difficult for attackers to infiltrate your systems.
???? Dede4d's Code: Dissecting the Threat
Dede4d has risen as a prominent risk within the cybersecurity arena. Experts are constantly examining its intricate code to uncover its true capabilities. Dede4d's arsenal seem to be remarkably adaptable, capable of conducting a wide range of malicious operations. Understanding its inner workings is essential to preventing the consequences it can inflict.
- Primary among Dede4d's attributes is its capacity to circumvent traditional security protocols.
- Additionally, it exhibits a distinctive level of stealth, making detection arduous.
- Dede4d's code is constantly being updated, suggesting the minds behind its dedication to remain a step ahead of defense analysts.
As a result, the cybersecurity sphere is competing to create new countermeasures to neutralize Dede4d's threats.
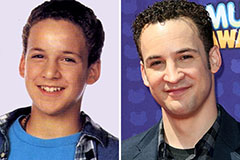 Ben Savage Then & Now!
Ben Savage Then & Now! Alisan Porter Then & Now!
Alisan Porter Then & Now!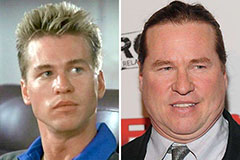 Val Kilmer Then & Now!
Val Kilmer Then & Now! Karyn Parsons Then & Now!
Karyn Parsons Then & Now!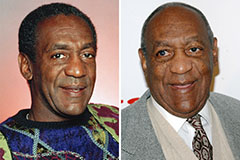 Bill Cosby Then & Now!
Bill Cosby Then & Now!